Quad9 Trends December 2022: Cyber Insights
A Monthly Insight into Quad9’s Top Blocks
Beginning in December 2022, Quad9 will begin releasing a monthly, in-depth report that explores the trending DNS lookups of malicious host names that we blocked during the prior month. Each month, Quad9 users will be able to download the entire report, which will provide a breakdown of several cybersecurity metrics, including but not limited to the prior month’s highest trending malware by volume of attempted domain access and type.
This type of information is valuable in that it further sheds light on the most prominent malware, phishing, spyware, and botnet threats that individuals and network administrators should be aware of. For Quad9 users, the information found in the monthly reports are more than supplemental intel surrounding trending cybersecurity and privacy threats. They should also serve as additional peace of mind that Quad9’s public and free DNS service is helping to provide its users with a safer, more private online experience.
Quad9 Identified Cybersecurity Threat Trends – November 2022
Last month, Quad9 observed a diverse array of threat categories. Among the many categories of threats blocked and analyzed were DDoS, Banking Trojans, Remote Access Trojans (RATs), and crypto-related malware. The graphic below represents Quad9’s analysis of the top ten malicious domains and their associated threats — which were blocked by Quad9.
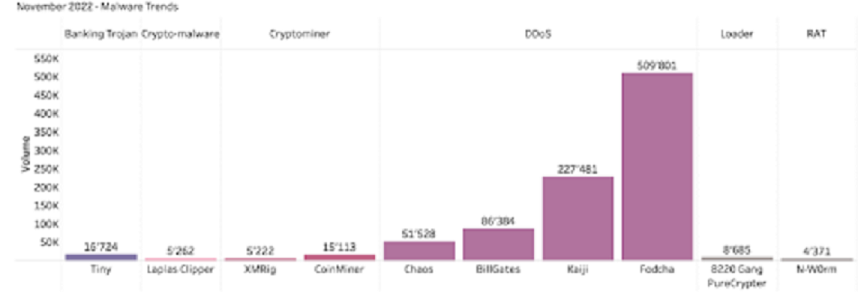
The graph above represents malware trends observed and blocked by Quad9 during November 2022. Due to the volume of DNS requests, Quad9 does not collect all the DNS requests, thus analyzed samples were recorded two times daily for the duration of 60 seconds. Source: Quad9.net
Quad9 determined that DDoS attack vectors continued an upward trend during the month. Among the top ten domains blocked by Quad9 in November 2022, four were attributed to DDoS malware.
Quad9 identified fridgexperts[.]cc as the domain which saw the highest number of prevented access attempts by users. This domain is attributed to Fodcha Command and Control (C2) server. Fodcha Command is a relatively new, yet powerful DDoS botnet, discovered by 360Netlab researchers in April 2022. This DDoS botnet has caused quite a stir within the cybersecurity community, as researchers report the latest version having grown to an unprecedented scale.
Although DDoS threats represented the most frequent access attempts during the month, they were far from the _only _cause for concern. Upon analysis of six domains with a high access attempt rate during the month, Quad9 observed several additional user threats that should also be monitored. The Tiny Banker Trojan was observed as the highest number of attempted access associated with api.peer2profit[.]global. This trojan infects end-user devices and attempts to compromise their financial accounts, ultimately stealing funds.
Quad9 also observed a higher number of attacks targeting cryptocurrency users, specifically those accessing clipper[.]guru, a domain attributed to the Laplas Clipper malware. This malware is designed to hijack cryptocurrency transactions by swapping a victim’s wallet address with the wallet address owned by threat actors. Lastly, the Quad9 team reported a high number of access attempts to x.rune-spectrals[.]com, which is attributed to a remote access trojan (RAT). This type of malware gives the attacker full administrative privileges and remote control of a target device.
The Takeaway
Quad9’s mission is to improve the security and stability of the internet, creating an ecosystem where users are less vulnerable to risks and more effective in their daily online interactions. By preventing connections to known malicious sites, Quad9 reduces exposure risks before they are downloaded to a device or before potential victims gain access to fraudulent websites.
Access the full December 2022 report.
References:
